Oops! You’ve been phished!
PLEASE KEEP READING. . .
This is an internal phishing campaign conducted by Netcracker’s Global Security Organization (GSO). Netcracker is required to conduct these tests as a requirement for ongoing compliance efforts.
Attackers send messages such as these in order to obtain sensitive information or install malicious software on your computer. In the future, you can spot a possible phishing email by looking for:
bad grammar/spelling,
urgent action required,
inconsistencies in sender email addresses/linked URLs,
requests for login credentials, and/or
enticing offers/incentives.

In the future, please be more cautious and block unsolicited emails right away by right-clicking the email > Junk > Block Sender (which will also delete the email).
Please reach out to securityincidentgroup@netcracker.com with any questions or to report a real phishing incident.
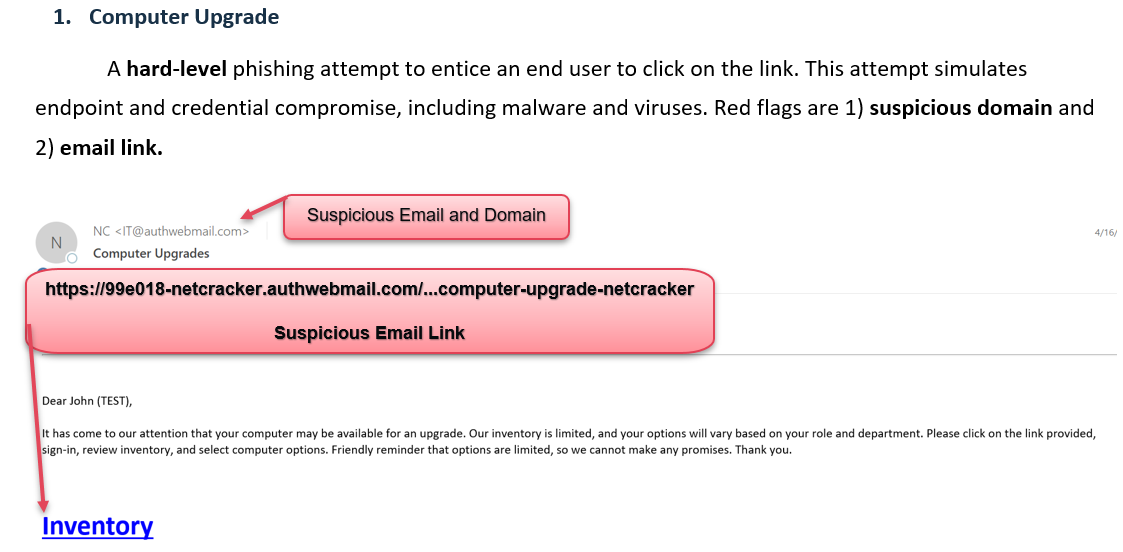
Take a look below to review the phishing email that you received to learn how to spot phishing attempts in the future:
Hard-level phishing attempts end users to click on suspicious links and provide domain credentials. This attempt is geared around credential compromise which includes an employee’s username and password. Noticeable red flags are 1) suspicious email/domain and 2) email link.
Example:
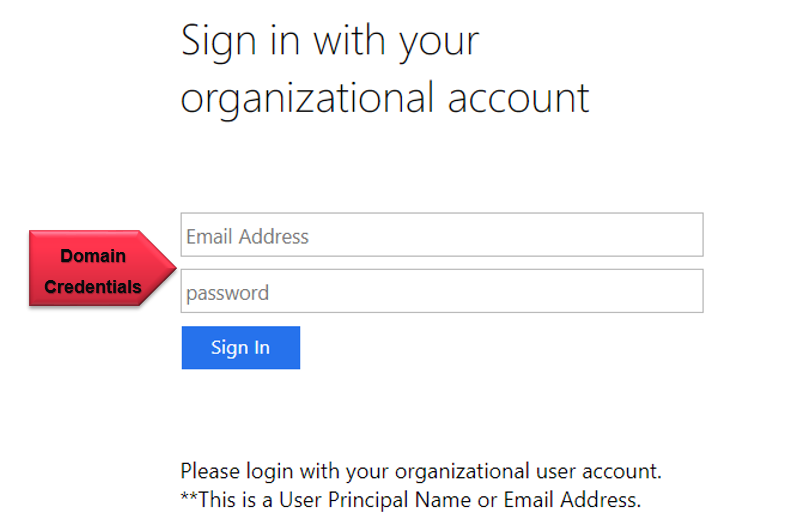
After end-users click the links, they will be directed to a generic sign-in displayed page below. When the password field has one character input the page will auto-direct to the official landing page letting the end-user know that they have been phished and that this is a training exercise by Netcracker.


.jpg)

.png)













